How to Import Data from XDR Platforms
You can import data into the / Forensic Acquisition and Investigation platform using an eXtended Detection and Response (XDR) system. / Forensic Acquisition and Investigation Host can be quickly deployed to compromised Windows and Linux machines via XDR vendors such as CrowdStrike, SentinelOne, and Microsoft Defender. However, macOS is not currently supported for SentinelOne and Defender integrations.
For detailed setup instructions, refer to the following pages:
Importing Data via XDR
Once the integration is set up, follow these steps to import data:
-
From within an investigation, click Import from XDR.
-
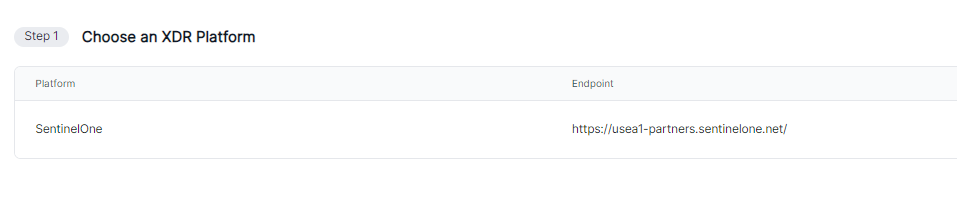
Select the XDR platform you have set up and click Continue.
-
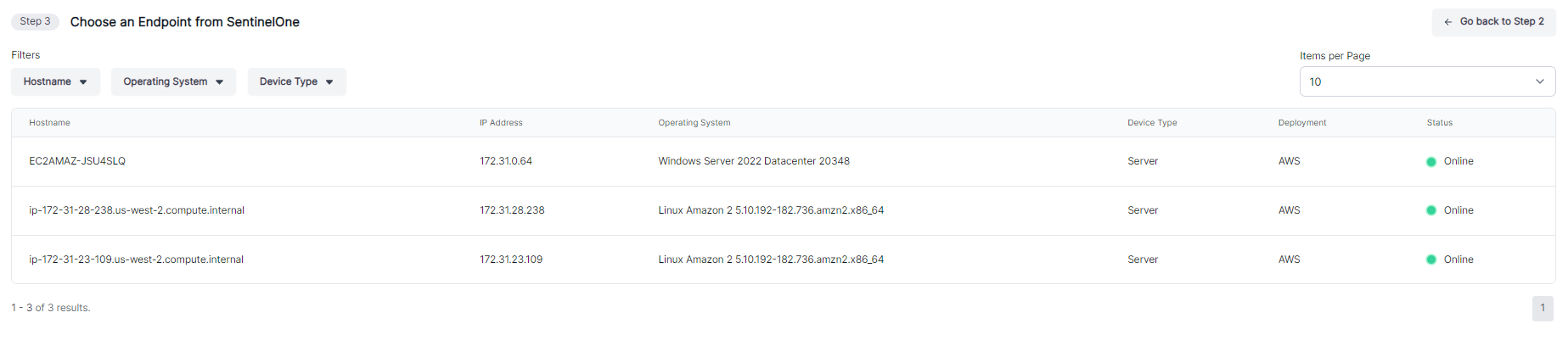
Search for or select the endpoint you want to collect data from, and click Continue.
-
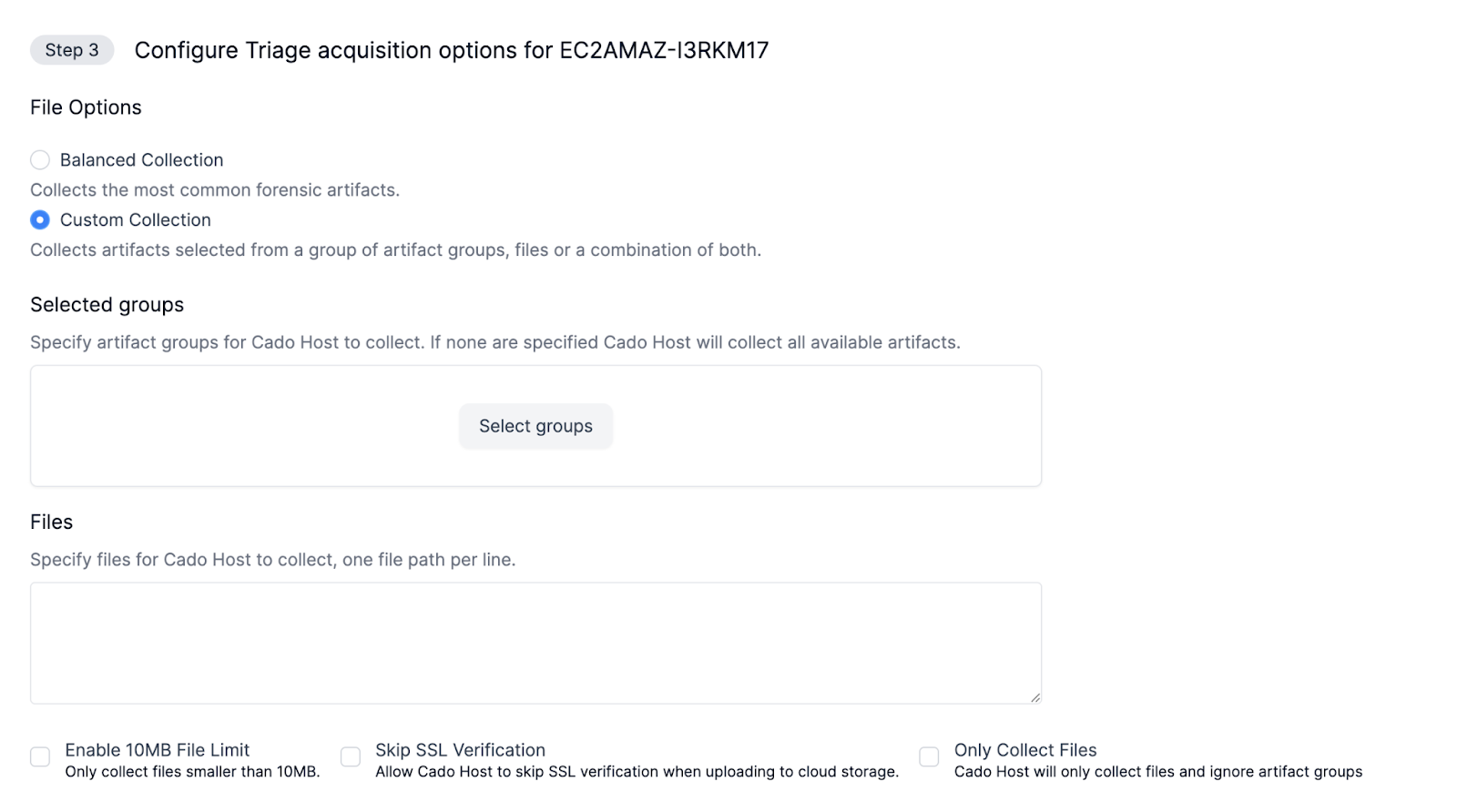
Configure the type of acquisition you would like to whether that's a balanced collection or a custom collection.
Balanced Collection - Collects most common artifacts.
Custom Collections - Able to customise your collection based on groups or filespaths or a mixture of both.
Groups - Filters collection to collect specific groups of files. Use the Groups Browser to see details about each group
Files - Choose to filter your collection based on specific filepaths
You can also set some parameters for your acquisition:
File Size Limit: Set the maximum file size to 10MB to prevent collection of larger files.
Skip SSL Verification: Disable SSL verification in collection parameters when necessary, understanding the security implications.
Collect Files Only: Select the "Only Collect Files" option to restrict collection to specified files and disable group filtering.
- Confirm your selections and click Start Import.
Once initiated, / Forensic Acquisition and Investigation will begin importing data from the selected endpoint via the XDR platform.
Automatic CrowdStrike Isolated Host Capture
You can capture data from a host that has been isolated within CrowdStrike. Previously this was a manual process as seen in the documentation below. How to enable Crowdstrike Isolated Host Imports
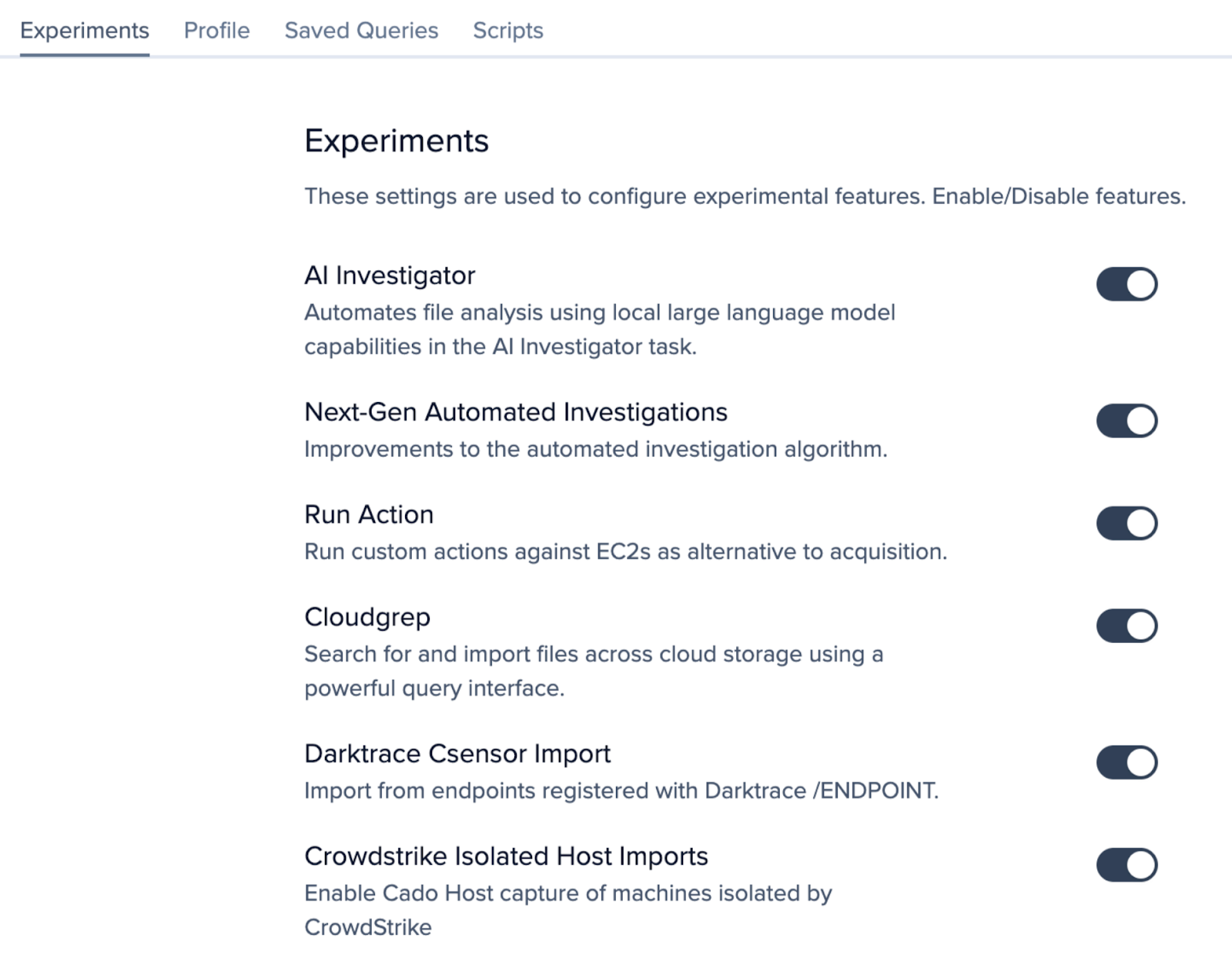
Once you have upgraded to version 2.297.0 navigate to Settings > Experiments then enable to setting for CrowdStrike Isolated Host Imports
CrowdStrike Quarantined Host Capture
In this section we will go through the steps required to manually perform a triage capture from your quarantined host on Crowdstrike to allow you to create an investigation within your cado platform.
Pre-requisites
- Access to RTR in the CrowdStrike console.
- Cado Host binary available for upload. The latest version is available within the platform at Import -> Cado Host.
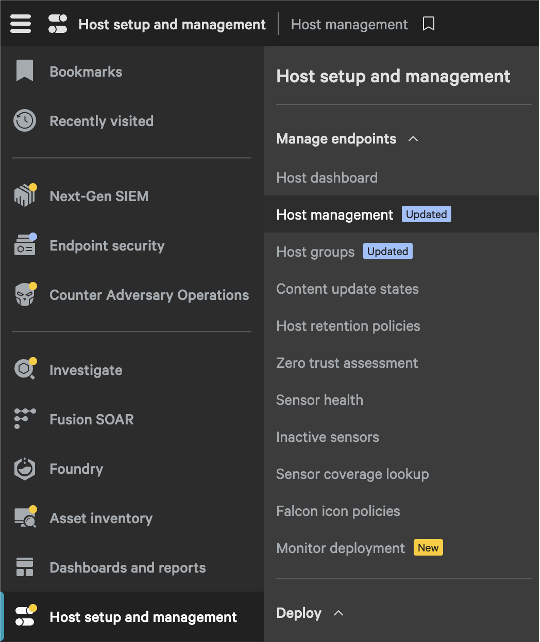
- Go to Host Management on your Crowdstrike console (/host-management/hosts)
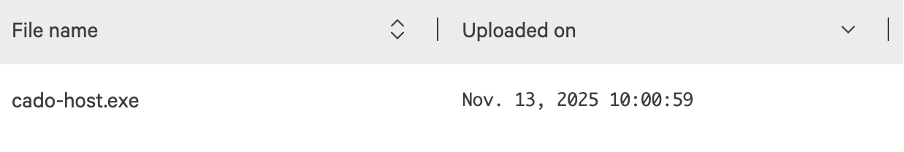
- Upload Cado Host Binary (/real-time-response/scripts/put-files)
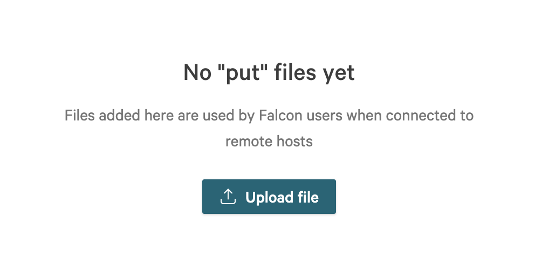
Once uploaded you will see the file on your “put file” list:
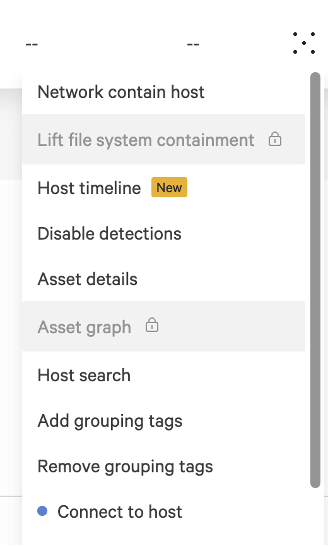
- Connect to Host
NOTE: The binary default directory is
C:\on Windows Hosts.
- On the host using Crowdstrike RTR run the command
put "cado-host.exe"
You will now be able to see the cado-host.exe in C:\
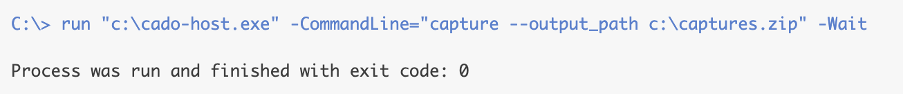
- Run the executable with the capture command:
run "c:\cado-host.exe" -CommandLine="capture --output_path c:\capture.zip" -Wait
If run successfully you will get the exit code 0
- You will now need to download the
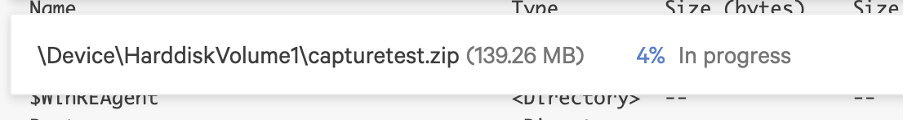
capturetest.zipusing the following command
get capturetest.zip
You will now see a progress banner for the zip download
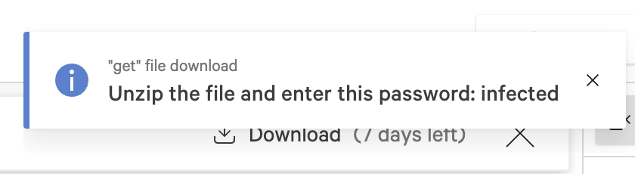
- Once the download has finished you will now be able to download the zip folder to your local machine
The zip folder will now be available to view on your default downloads location on your local machine. You will be prompted to enter a password which will be shown on the Crowdstrike UI:
- Use the AWS CLI to upload your file directly to your S3 bucket by using the below command:
aws s3 cp capture.zip s3://your-bucket-name/path/
- Please follow this document to import your data from S3 into your Cado Platform.